Strava: The Nuclear Carrier Is Over Here – Come and Get It
Strava has a problem. It is not new. It is not getting fixed. And if you use Strava, it is worth understanding why.
This Has Happened Before. Many Times.
- 2017 — Strava releases its Global Heatmap. Three trillion GPS points, publicly visible. Nobody notices anything unusual at first.
- 2018 — Analyst Nathan Ruser notices the heatmap is glowing in remote deserts. Those glowing lines are US secret bases and patrol routes in Syria, Iraq and Afghanistan. French bases in Niger are exposed too. The Guardian, NYT and Wired report it. The US Department of Defense bans fitness trackers on deployment.
- 2018 — French military personnel at the Île Longue nuclear submarine base in Brest are already logging runs on Strava. Local paper Le Télégramme reports it. Nothing changes.
- 2020 — Bellingcat’s Nick Waters identifies 14 SAS soldiers at the top-secret Hereford base using only their public Strava profiles.
- 2022 — Israeli NGO FakeReporter plants fake Strava segments inside six top-secret Israeli bases. 100 individuals are exposed, including Mossad personnel. The fake segment method bypasses even private account settings.
- 2023 — Russian submarine commander Stanislav Rzhitsky is tracked and killed during his regular Strava run in Krasnodar. Ukrainian intelligence chief Budanov likes his final upload.
- 2024 — Le Monde’s StravaLeaks investigation reveals that bodyguards of Macron, Trump, Biden and Putin have all exposed leader locations and movement patterns through public Strava profiles.
- 2025 — French nuclear submarine crew at Île Longue log runs on Strava, revealing patrol schedules, timings and personnel identities. Their smartwatches bypass the facial scanners and phone checkpoints at the base entrance. The French Navy calls it a problematic situation but not a major risk.
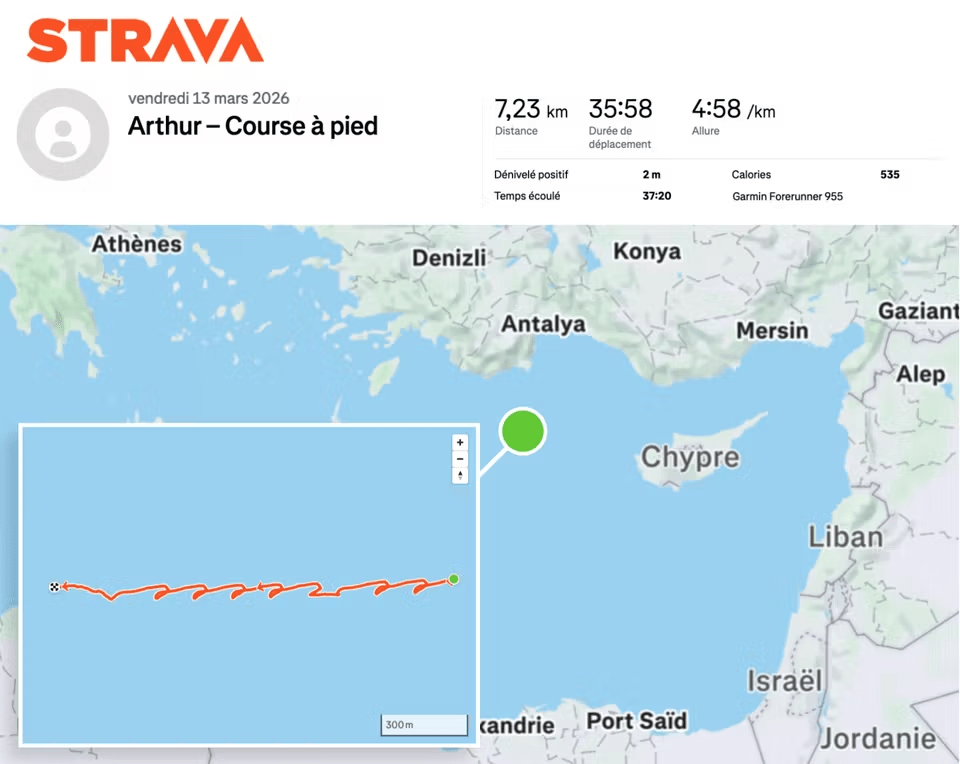
- 2026 — A French naval officer logs a 36-minute, 7km deck run on the aircraft carrier Charles de Gaulle. His public Strava profile broadcasts the carrier’s exact position in the Mediterranean in near real time. Le Monde verifies it against satellite imagery captured 90 minutes later. The carrier and its escort vessels are visible.
- 2026 – UK military personel near the Fastlane nuclear base have their whereabouts exposed on STRAVA.
What Strava Exposed This Time
The Charles de Gaulle’s general presence in the Mediterranean was not secret. France announced the carrier strike group’s deployment to the region in earlier this month, days after the outbreak of conflict involving Iran. What was not public was its precise location — northwest of Cyprus, roughly 100 kilometres from the Turkish coast, operating near a conflict zone in which Iranian strikes had already targeted French assets and UK assets on Cyprus.
The Strava upload changed that. The data was live within minutes of the run ending. The GPS trace of the deck run placed the carrier exactly and the escort vessels’ positions could easily be inferred..
How It Happened
On 13 March, a young French naval officer finished a training run on the deck of the Charles de Gaulle and synced his smartwatch. His Strava profile was set to public — the app’s default. The activity was uploaded automatically. It showed a looping 7km route that could only have been run on a ship deck, timestamped and geotagged to a precise location in the eastern Mediterranean.
He was not trying to leak anything. He was logging a workout.
Why Strava Keeps Getting Caught In These Stories
Strava’s default setting is public. Always has been. Most users never change it. The platform aggregates data even from accounts set to private via its Global Heatmap. Its segment feature, as the Israeli case demonstrated, can expose individuals even when they believe their account is protected.
Military organisations have known this since 2018. The US DoD acted. Many others issued guidance. But guidance is not enforcement, smartwatches are not phones, and a sailor who wants to log a PB on a deck run is not thinking about operational security. He is thinking about his time.
Strava’s position, consistently held since 2018, is that privacy tools are available and it is the user’s responsibility to use them. That is a defensible position for a fitness app. It becomes harder to defend when the same failure mode has now exposed secret bases, nuclear submarine schedules, world leader movements, and an aircraft carrier in a conflict zone — across eight years and multiple countries.
What Happens Next
After 2018, the US DoD reviewed its policies. France issued guidance. The UK issued guidance. Israel tightened rules after the Hereford and Mossad incidents. The French submarine base at Île Longue was reported as a problem in 2018 and again in 2025, with the same personnel, the same app, and the same outcome.
The honest answer to what happens next is: probably not much. The structural problem — a public-by-default fitness platform used by millions of people who happen to work in sensitive environments — has not changed in eight years. Individual incidents produce individual responses. The pattern continues.
Is This Strava’s Fault? And Does It Matter Right Now?
Strava clearly did not design its platform to expose military assets. Its users chose to use it in places they should not have. They may have been ordered to make their activities private (as per guidelines), but have been careless in following them. Every one of these incidents was a user error in the narrowest sense.
That said, the platform design has consequences. Defaults matter, and Stava is responsible for the defaults. A platform with 135 million users, default-public settings, and a known, documented, repeated history of military security failures has a reasonable case to answer about whether those defaults are appropriate, especially at a time when America is at war, and Strava is an American company.
That question is arriving at an awkward moment. Strava has been strongly rumoured to be moving toward an IPO. The company has spent years building its brand around community, performance and aspiration. Being the platform that keeps finding warships is not the identity it seeks in a pre-IPO window. Whether this incident accelerates any rethinking of default privacy settings — the one change that would actually matter — remains to be seen.
For now, somewhere in the eastern Mediterranean, a carrier strike group is hoping nobody else on board is due a long run.
Last Updated on 7 April 2026 by the5krunner

tfk is the founder and author of the5krunner, an independent endurance sports technology publication. With 20 years of hands-on testing of GPS watches and wearables, and competing in triathlons at an international age-group level, tfk provides in-depth expert analysis of fitness technology for serious athletes and endurance sport competitors.

Love this content.
It’s obviously not Strava’s fault necessarily – it’s the fault of the dummies that are using it. Same could be said if they had location sharing set up on their Instagram accounts. The slight difference is that Strava is more niche, but it’s also the exact kind of app that people in these positions (fit, capable individuals – not to mention competitive, so Strava is catnip for them) will use.