519 UK Military Personnel Exposed at Nuclear Bases Through Strava
Two weeks after a French naval officer broadcast the precise location of the aircraft carrier Charles de Gaulle through a public Strava upload, an investigation by The i Paper has found 519 officers, contractors and family members doing the equivalent across five of the United Kingdom’s most sensitive military installations. One of the exposed running segments is publicly titled “Security Breach” on the platform. It remains visible.
This is the same problem, in the same country, on the same platform, eight years after it was first reported.
The Investigation
The i Paper examined public Strava data logged at UK military sites since January 2026. The findings cover 519 individuals — officers, contractors, intelligence staff and their relatives — who recorded exercise activity within restricted military perimeters with their accounts set to public. The investigation identified personnel by name, mapped their home addresses through linked profiles, and in at least one case traced an individual to the specific nuclear submarine they were assigned to.
Five Bases, Five Categories of Risk
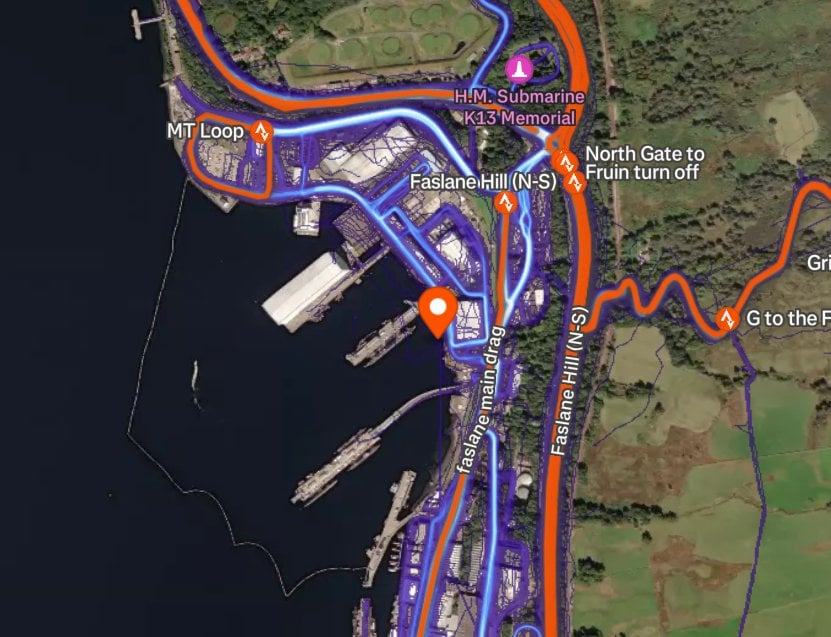
HMNB Clyde, Faslane. One hundred and ten individuals have logged public runs at the Faslane naval base since January. Faslane is the home of the UK’s Trident nuclear deterrent. One route logged inside a restricted area of the site contained sufficient detail to identify the specific nuclear submarine the individual was deployed on. A separate account at the same base posted photographs of warships entering the Scottish port, including the arrival of a US Arleigh Burke-class destroyer. The families of submariners were identifiable through linked Strava profiles. The timing carries additional weight: an Iranian national and a Romanian national were charged last month after allegedly attempting to enter the base by force.
Northwood. The UK military’s central command headquarters. A senior source based at the facility told The i Paper that the publicly visible data amounts to “damn good intelligence for the enemy” and that the exposure creates a direct risk of blackmail and coercion of personnel and their families.
RAF Fylingdales, North Yorkshire. The only installation in the UK equipped with an early warning system for ballistic missile launches. Engineers at the base were identifiable through their public Strava activity.
RAF Akrotiri, Cyprus, and Diego Garcia, Indian Ocean. Personnel at both overseas bases were traceable through the app. Both have been directly involved in operations against Iran. Both have been targeted by Iranian strikes in recent weeks. The i Paper identified active-duty personnel at each location through their public profiles.
One joint UK-US installation. Not named in the investigation, but a running route within the secure perimeter has been publicly titled “Security Breach” on the platform. The route remains live.
The Pattern of Life Problem
Military intelligence analysts call it pattern of life analysis. It is among the oldest methods in the profession: observe the movements, rhythms and habits of a target over time until predictive intelligence becomes actionable. Strava generates that analysis automatically and publishes it to anyone who searches for it.
Strava has 135 million registered accounts and is an official data partner of mass-participation events including parkrun, which hosts over four million participants across more than 900 locations in the UK alone. Its users skew toward the fit, the competitive and the habitual — precisely the population that fills the armed forces. A sailor who wants to log a personal best on a base run is likely thinking about his time rather than operational security.
The result is a platform that produces, automatically and without intent, what security services call a pattern of life. Enough public runs clustered around a military installation create a map of routine, identity and movement. Enough linked profiles reveal family names, home addresses and social connections. The intelligence value depends on accumulation.
Security expert Dan Lomas told The i Paper: “The fact that individuals are using personal accounts in a restricted area allows foreign states to piece together small pieces of information that you can potentially build up about an individual’s life.”
A UK military intelligence official, approached separately, described the volume of publicly visible data as “frankly ridiculous.”
The MoD Response and the MP’s Assessment
The Ministry of Defence issued a statement saying it takes personnel security seriously and keeps guidance under constant review. On the specific question of operational risk, the MoD suggested that fitness app activity does not constitute an operational threat because the locations of the bases are already in the public domain.
Security analysts disagree with that framing. Yes, the locations are known but the personnel are not. Submarine assignments, movement patterns, family addresses and the identity of intelligence staff at Fylingdales are only in the public domain because Strava puts them there.
Conservative MP Ben Obese-Jecty, a former army officer, said the situation “beggars belief.” He noted that he stopped using Strava when he became an MP and had locked down his profile before that. He added that Strava provides sufficient privacy controls and questioned why armed forces personnel failed to apply them “given the current, and very real, threat posed by sub-threshold activity from our adversaries.”
What Has Not Changed Since 2018
The Faslane base appeared in the original 2018 Global Heatmap investigation. It appears again here. The US Department of Defense responded to the 2018 incident by banning fitness trackers on deployment. France issued guidance. The UK issued guidance. In 2022, Israeli NGO FakeReporter identified Mossad personnel through planted Strava segments, demonstrating that even private accounts are not fully protected by the platform’s architecture. In 2025, French submarine crew at Île Longue were found logging runs that revealed patrol schedules. In March 2026, a French naval officer revealed a carrier’s position in a live conflict zone. Now this.
Guidance and enforcement are two different things. Smartwatches pass through base security checkpoints without triggering the controls that apply to mobile devices. The structural problem remains — a public-by-default fitness platform used by millions of people who happen to work in sensitive environments.
Strava’s default setting is public. It has been since the platform launched. The one technical change that would materially reduce recurrence — making new accounts private by default — remains outstanding. Strava is widely reported to be preparing for an IPO. Being the platform that keeps finding nuclear bases is not the association it needs in a pre-IPO window.
Whether this incident accelerates a rethinking of default privacy settings remains to be seen. What is clear is that 519 people at the UK’s most sensitive military sites were publicly broadcasting their locations and identities on a fitness app this year — and one of them thought it was funny enough to say so in the title of the route.
Last Updated on 6 April 2026 by the5krunner

tfk is the founder and author of the5krunner, an independent endurance sports technology publication. With 20 years of hands-on testing of GPS watches and wearables, and competing in triathlons at an international age-group level, tfk provides in-depth expert analysis of fitness technology for serious athletes and endurance sport competitors.

Not Strava is exposing military personnel, military personnel are exposing themselves.
This headline is clickbait.
if you think that’s clickbait this must be the first article you’ve read on the internet or in a newspaper.
as per the artcile: “Strava’s default setting is public. It has been since the platform launched. The one technical change that would materially reduce recurrence — making new accounts private by default — remains outstanding.”
by default they are exposed. I agree, the personnel could be more careful.